As WannaCry’s ransom deadline approaches for tens of thousands of cyber victims around the world, many would agree that global cybersecurity has not kept pace with the complexity and virulence of attacks. The hacking of American and French electoral candidates, theft of NSA malware tools, and subsequent ransomware attack have shaken the world out of its complacency.
While Congress considers restricting the NSA through the recently introduced PATCH Act mandate, the US and its allies should set their sights on quantum cybersecurity, which employs the properties of quantum physics to secure data. Most of the world's electronic data is protected by sophisticated encryptions which can only be unlocked with the correct numeric key. The quantum-enhanced version of this technology is believed to be impregnable, and can be viewed, with a small amount of irony, as a three-piece Russian nesting doll.
Quantum cybersecurity's “outer shell” is the physical infrastructure that electronic information and numeric keys are travelling across, usually fiber optic networks. Built correctly, quantum key distribution ensures the information sent over these networks is unhackable because it travels in quantum states, such as single photons or lasers. Because such networks are governed by the principles of quantum physics, the quantum particles carrying the data would change their physical state if someone attempted to hack or observe them, thereby halting the transfer of information and alerting the users of an attempted hack. Quantum key distribution would provide the highest level of protection for exchanging keys and sensitive information between both classical and forthcoming quantum computers.
The numeric keys also require robust encryption to ensure they’re securely exchanged. There has been an on-going race between encryption approaches and hacking capabilities, with each side grappling for the upper hand. The method commonly used today, asymmetric encryption, will eventually be overpowered by quantum computers, which is why quantum resistant algorithms are currently being developed. While this technology is about five years from adoption, quantum resistant algorithms can be incorporated into the quantum network technology that exists today.
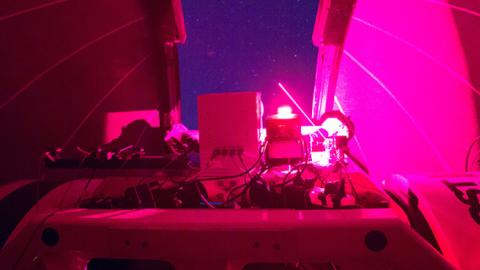
The final layer of protection at the heart of quantum cybersecurity is the ability to generate truly random numbers, the world’s strongest keys. Yet true randomness cannot be developed from software or anything man-made, and can only be found by measuring a physical state. Scientists use sensitive instruments to listen to the crackle of energy in the fabric of the universe, which spontaneously creates and self-destructs. Quantum physicists harness this “quantum noise” and convert it into a stream of true random numbers. This technology is already being implemented today, with a handful of banks, governments, defense sectors, and private cloud carriers as early adopters.
Around the world, governments and private sector are starting to develop quantum technology. The United States government commits around $200 million a year to quantum research, along with heavy investment by the private sector. Australia, a hotbed of quantum research, is leading the efforts with the world's fastest true quantum random number generator, being developed by Quintessence Labs. China is making strides in secure quantum communications, laying claim to the world’s longest quantum network and the world’s first unhackable quantum satellite. The European Union has committed to contributing one billion euros to their flagship quantum research project, while Canada begins a joint venture with the University of Waterloo to construct a quantum microsatellite.
The recent WannaCry attacks have exposed a dangerous truth: the frontlines of the information age have been vulnerable for too long. Quantum cybersecurity carries the potential to fortify the infrastructure of our institutions, such as electronic polling stations, hospital computers, energy grids, and sensitive government files. While in varying stages of development and adoption, governments and businesses can leverage quantum cybersecurity technology, not compete with it.