Late last week the White House released America’s first comprehensive National Cybersecurity Strategy in fifteen years. Fifteen years is the cyber equivalent of a geologic epoch, because the challenges and technologies in this arena evolve almost monthly. Nonetheless, America finally has the cybersecurity strategy it needs and has been waiting for. The only question is how best to implement it.
Barack Obama promised a strategy like this during his 2008 presidential campaign. But after eight years in office during which we suffered two devastating cyberattacks--one against Sony Corporation directed (almost certainly) by North Korea in 2014, and the other almost certainly by China against the Office of Personnel Management in 2015 which purloined the records of twenty-two million past and present government employees--Obama gave us plenty of talk, including eighteen executive orders and a much ballyhooed Cybersecurity National Action Plan, but almost no action, including against the worst cyber offenders.
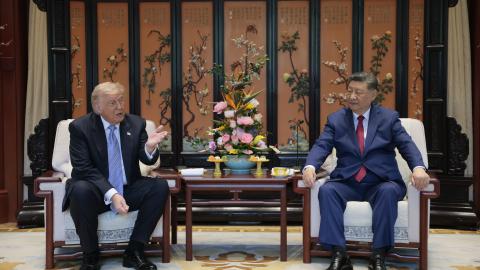
In less than 18 months the Trump administration has come up with the kind of holistic and proactive approach to our cybersecurity vulnerabilities that many of us have been arguing for since the mid-2000’s. For the first time we have a U.S. government that acknowledges this problem is not going away until we realize that it’s the most serious economic as well as national security threat, of our time.
As the plan itself says in its introduction:
“The Administration recognizes that the United States is engaged in a continuous competition against strategic adversaries, rogue states, and terrorist and criminal networks. Russia, China, Iran, and North Korea all use cyberspace as a means to challenge the United States, its allies, and partners, often with a recklessness they would never consider in other domains. These adversaries use cyber tools to undermine our economy and democracy, steal our intellectual property, and sow discord in our democratic processes.”
In short, the plan recognizes that in cyberspace we are fighting a multi-front war. The current furor over Russian “meddling” in U.S. elections is only one part of a concerted effort by our leading foes to weaponize that space. America’s response must be appropriate to the threat.
For that reason, the strategy makes clear that cyber theft represents a major attack on our economic well-being as well as our national security. As my most recent forbes.com column pointed out, China has plundered American—owned intellectual property by cyber theft and other illicit means to the tune of $225 and $600 billion annually. It’s time to develop a national plan to secure that intellectual treasure trove; strengthening our cyber defenses in the public and private sectors will go a long way to accomplishing that.
The White House also recognizes the longer-term problem of building a workforce ready and capable for cyber response. As I have also pointed out in this space, when only twenty-one percent of computer science majors and graduate students in our universities are actually American nationals, we have an issue needs the full engagement of the federal government as part of implementing a comprehensive cybersecurity strategy.
Finally, the plan also recognizes that in the long term we need to deal with the challenge of future quantum technology. As it points out:
“Public key cryptography is foundational to the secure operation of our infrastructure. To protect against the potential threat of quantum computers being able to break modern public key cryptography, the Department of Commerce, through the National Institute of Standards and Technology (NIST), will continue to solicit, evaluate, and standardize quantum-resistant, public key cryptographic algorithms. The United States must be at the forefront of protecting communications by supporting rapid adoption of these forthcoming NIST standards across government infrastructure and by encouraging the Nation to do the same.”
Unfortunately, waiting for NIST to arrive at those standards may not be enough. Its timeline is leisurely compared to the quantum threat; it envisages an implementation and rollout that may not finished until 2034—while a quantum computer able to crack our public encryption systems could be ready more than a decade before that.
Fortunately, there is plenty of room for the private sector to step up and take the lead for NIST to follow, not just in quantum-resistant algorithms, but also in using quantum technology itself to safeguard data and networks, through state-of-the art hardware such as quantum random number generators and the use of quantum key distribution.
Several government officials with whom I’ve discussed the matter have been reluctant to address funding future quantum-based cryptographic systems, perhaps for fear that this will divert attention from more urgent matters to farther technological horizons.
That fear is misplaced. The quantum computer threat to our public encryption systems is coming sooner than we realize. “The moral equivalence of war” may be a shop-worn phrase. But when it comes to the nation’s cybersecurity threat today and tomorrow, and the threat to our allies, it’s an appropriate one. The new National Cybersecurity Strategy clearly points the way forward. Now we need the right people, from the White House and Congress to the private sector, to lead the way, as well—not just today but far into the future.