Protecting US Communications: Strengthening Supply Chains and Countering Foreign Risk


Director of the Federal Communication Commission’s Council on National Security

Chief of Staff, Enforcement Bureau, Federal Communication Commission

Deputy Chief, Office of Engineering and Technology, Federal Communication Commission
Chief, Public Safety and Homeland Security Bureau, Federal Communication Commission

Chief, Office of International Affairs, Federal Communications Commission


Foreign-controlled telecommunications infrastructure and vulnerable global supply chains pose growing risks to the integrity and security of US communications networks. The Federal Communications Commission has taken steps to address these challenges over the past year. Efforts have focused on rooting out non-compliant overseas “bad labs” from the FCC’s equipment authorization program, accelerating the buildout of submarine cable systems, and mitigating risk from high-risk foreign components.
Marking the one-year anniversary of this initiative, this event will highlight the FCC’s progress and examine next steps to secure communications supply chains and mitigate emerging risks. Experts and policymakers will discuss how to close regulatory gaps, improve compliance, and build more resilient and trusted infrastructure.
2:00 p.m. | Fireside Chat
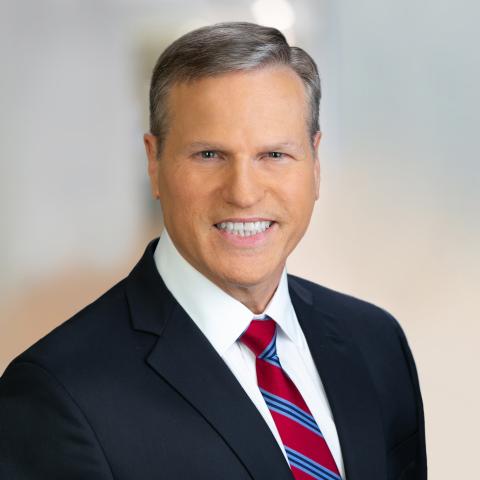
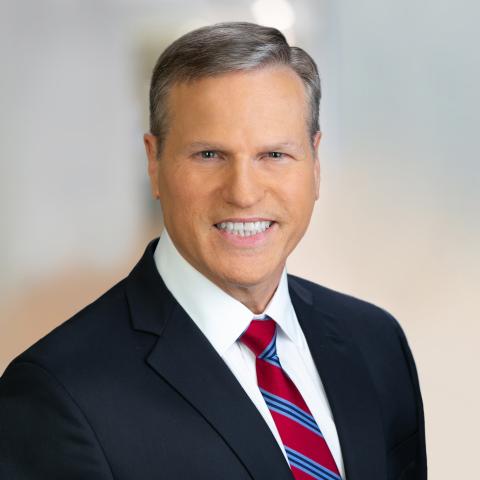
Moderator: David Feith, Senior Fellow, Hudson Institute
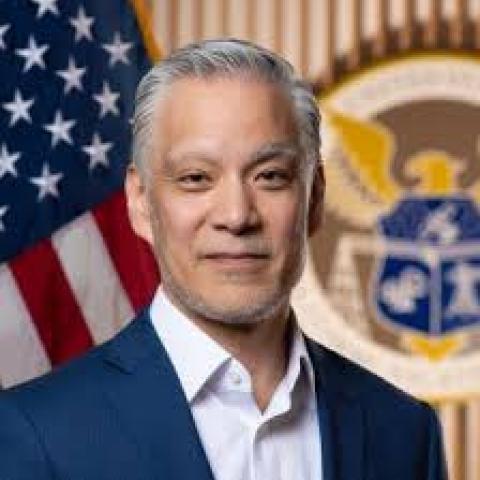
· Adam Chan, Director of the Federal Communication Commission’s Council on National Security
3:00 p.m. | Panel Discussion
Moderator: Michael Sobolik, Senior Fellow, Hudson Institute
· Hunter Deeley, Chief of Staff, Enforcement Bureau, Federal Communication Commission
· Alice Jou, Deputy Chief, Office of Engineering and Technology, Federal Communication Commission
· Zenji Nakazawa, Chief, Public Safety and Homeland Security Bureau, Federal Communication Commission
· Thomas Sullivan, Chief, Office of International Affairs, Federal Communications Commission
Listen on Spotify and Apple Podcasts.
Fireside Chat
David Feith:
Thank you, everyone for gathering, thank you to Hudson for hosting us, and thank you to our FCC colleagues for joining us for a really interesting discussion. I note that we have some folks in the crowd who are real experts on the FCC, and obviously, a really rare opportunity to hear from a large number of the folks who set and implement the important policies of the FCC. We’ll start with Adam Chan, who is the inaugural director of the FCC’s Council on National Security. The occasion for this event called Strengthening Supply Chains and Countering Foreign Risk is the one-year anniversary of the creation of this Council on National Security by Chairman Carr and his team at the FCC. And it is led by Adam, who is Chairman Carr’s senior advisor on national security matters.
Adam joined the FCC from the Boyden Gray PLLC law firm. Before that, he worked on the hill as a national security legal fellow on the House Select Committee on the strategic competition between the United States and the Chinese Communist Party. Before that, Adam graduated from the University of Chicago and Columbia Law School. And so, he represents evidence that a Columbia degree does not yet render one unemployable. And we’re very glad to have him on the occasion of this anniversary. And so, I’d suggest that we start there. Adam, tell us if you would, about the Council on National Security, about its origin, its purpose, some of its statutory grounding, and what you’ve been up to.
Adam Chan:
Yeah, no. I guess first, thanks to you, thanks, Hudson for hosting. Thanks to you all for coming. It’s great to be here to be able to discuss some of the FCC’s national security work. As you all may have seen, been a lot more active over the past year plus than in the past and I definitely expect that to continue. I think to talk about the Council on National Security, this was one of Chairman Carr’s first initiatives when he first became chairman. When he was announced as chairman, he knew he wanted national security to be a top priority of his chairmanship. He asked me to come on to be kind of his point person on all things national security, which is sort of a novel position. In the past, a lot of the sort of chairman’s advisors have been sort of divided according to specific bureaus or specific technology areas.
We also quickly realized that it made sense to establish this new Council on National Security, which is this body that has features members, staff, leadership from all the different relevant FCC bureaus and offices. You’re going to hear from a lot of the national security leaders on the council later today. But rather than having sort of the national security work streams be siloed in, say, the Wireline Bureau or the Public Safety Bureau or the Office of International Affairs or Public Safety Bureau, like to actually instead integrate all the sort of different national security functions within a sort of one body to both sort of harmonize rules and sort of coordinate a unified agenda on national security questions that can both allow us to get more done, also sort of rationalize the process. So, a lot of the different actions the commission is taking all make sense together.
I think one sort of notable piece of this new Council on National Security is we’ve also, to a much greater extent, integrated both the general council’s office and the Enforcement Bureau, which you’ll hear from on the panel along with the sort of policy related functions, such that our enforcement actions inform our rulemaking actions and vice versa. But as you’ve probably seen, we’ve been able to get a lot done through this model. We think it’s working well. We think it’s sort of helped develop a kind of cadre of national security experts throughout the commission and sort of really encourage some good kind of collaboration.
David Feith:
Tell us a bit about the mechanics. I mean, we will have a great opportunity after this discussion to hear, as Adam noted, from four of the leaders who participate in the council and represent different . . . Of the bureaus of the FCC. You’ve suggested a little bit about the importance of the design of integrating those national security functions that had been otherwise spread out across the different components of the FCC. Perhaps in addition to that, what about the interaction of the Council on National Security with the rest of the interagency? What is the process? Is it regularized? Is it ad hoc? Who are the main interagency counterparts across that vast divide between ostensibly independent agencies and the rest of the executive branch?
Adam Chan:
Right. So I think, one, I guess, sort of process internally within the FCC. I think it’s very much both a sort of top down and bottom up in the sense that there are a lot of ideas that come from me, from Chairman Carr, from our discussions, also a lot of ideas that originate from staff or from the bureaus, either on things they’re working on or otherwise. And I think that’s all to the good.
Additionally, I think as the FCC has done more in the national security area, the FCC is also sort of more closely integrated than ever with our national security counterparts throughout the broader administration, whether that’s, for example, Team Telecom, which is an interagency body led by DOJ National Security Division that advises us on national security questions, whether that’s the ICTS office at the Department of Commerce, whether that’s even agencies such as the intelligence community, as well as the economic agencies that have been sort of central in a lot of the kind of foreign policy decision making, such as USTR and Treasury, that we often coordinate closely with them as we issue rules or engage in adjudications that have implications, both sort of economically to other national security issues or to our sort of international relations. I think we’re also regularly coordinating with the White House and the different sort of White House components there, as well as they sort of drive a broader national security agenda within the administration and see how we can fit in with that.
David Feith:
Tell us a bit about the toolkit and especially the covered lists. I mean, this is an institution that is of relatively recent vintage and we’ve heard and read a good bit about it over the last year. It stands out as one of a small number of really important new innovations in the kind of national security policy and technology policy toolkit of the inner agency. You mentioned ICTS and Team Telecom, both of relatively recent vintage also. So, what is the covered list? How does the council use it, and how does it fit within a broader range of tools, perhaps more longstanding ones that the FCC also has?
Adam Chan:
Yeah, no, I guess to sort of start maybe at the beginning, back in 1934, actually, Communications Act of 1934 that first established the FCC, in section one of the Communications Act, it set up the commission, set two purposes. The first is to expand access to communications technology, and then the second is for the purpose of national defense. So, when the FCC, what’s originally set up, was originally envisioned as very much a national security agency. And so, to a large extent, some of the more recent action the FCC has taken over the past, say, five, seven years, as well as over the last year, are very much a return to the FCC’s roots as a core national security agency.
The FCC has a lot of longstanding tools in the national security space, whether that’s just sort of broad kind of public interest, regulatory authority over telecommunications within the US, whether it’s the Cable Landing License Act that gives us authority over undersea cables that land in the US. I think the covered list sort of stands out as a particularly interesting and kind of unique set of legal authorities, really a product of two pieces of legislation. First, the Secure Networks Act in 2019 established the covered list, which is basically a list of communications equipment and services that have been determined to pose unacceptable risks to the national security of the United States or safety and security of US persons.
The legislation also establishes ways that equipment or services can be added to the covered list. Sort of uniquely, the FCC, we cannot ourselves add to the covered list, so this makes it very different than say other national security lists that go around sort of other agencies where, say, treasury maintains sanctions lists that treasury itself can add new targets to. And so instead, we rely on other enumerated either national security agencies or interagency bodies to actually make the determinations to get added to our covered list. Originally, as set up through that statute, the covered list did not actually have a great deal of legal significance. There were some restrictions on specifically in telecom networks that received FCC subsidies, that they couldn’t keep receiving funds if they had covered equipment in their networks. This also was sort of tied into the broader rip and replace agenda for certain untrusted technologies in US telecom networks.
I think the covered list really got new teeth in 2021 with the passage of the Secure Equipment Act, which prohibited FCC authorization for any equipment listed on the covered list. So of note here, this goes back to a much older authority the FCC has, but in order to import or sell almost any electronic device, really any device that emits radio frequency, which is almost any electronic device, you need FCC authorization. So that’s everything from computers to phones to drones to modules to . . . What have you. You’ve probably seen the FCC sticker on your devices.
But now with the Secure Equipment Act, this means that the FCC can’t authorize new models of any of the devices on the covered list for import or sale in the United States. So, it’s a functional prospective ban from the US market. So that is sort of powerful tool and say sort of briefly the sort of initial few things that were added to the covered list were kind of entity-specific. So number one is telecommunications equipment and services produced by Huawei, and there were several others like that. Recently, in the last few months, the administration has taken a different approach to sort of target sort of potentially whole technology sectors as national security threats based on the production location, rather than the sort of specific entity that is producing or providing the equipment or services.
David Feith:
Let’s talk about the sector, starting with drones. What is the action taken on drones, what was its genesis, and what’s happened in the four or five months since you all took action?
Adam Chan:
Yeah, no. So, drones obviously has been on the radar for US sort of national security experts, administration officials across administrations for a long time now. I think what happened here, once again, this is not sort of . . . The FCC, we did not sort of wake up one day and decide, “We want to do this.” This was a broader, you know, the product of an interagency body that made a determination to update the covered list, because there was certain UAS, unmanned aircraft systems, related critical components that posed unacceptable risks to the national security of the United States that also identified all sort of equipment and services produced by sort of two other companies, like leading drone companies as well, that they were identified specifically. But notably, this expanded it to any drone or drone component produced in a foreign country. The national security determination explained there were basically two risks involved with these technologies.
One is a sort of kind of traditional like national security risks involved, whether it’s that’s espionage and surveillance, think drones flying over military bases, disruption to major events. Again, think World Cup or FIFA or something like that. So some sort of obvious use cases, as well as sort of economic security justification that . . . Look, drones are critical to warfare today, and drones are also critical to sort of modern future economy, and so it’s important for the US to have a trusted drone supply chain here at home. So I think those sort of considerations that led to the determination to add drones to the covered list, there have subsequently been some exemptions there. One is sort of if you’re on the sort of military’s blue UAS list, list of drones that are approved for sale to the military, if you meet the Buy America domestic end product standard, as well as if you get conditional approval from the Department of War or Department of Homeland Security, it’s basically sort of an individualized waiver process.
So, through that, I think since then, the FCC, we’ve been implementing this. We’ve not been sort of approving covered drone models since then. I think we think it’s gone very well. So far, I think there have been sort of billions of dollars announced in investment deals in the US, thousands of jobs created. And so, we think that this is actually sort of working well, where this is sort of potentially crowding in private capital into America to invest, even as sort of more dangerous devices are sort of gradually phased out over time. And so we’ve obviously been sort of proactively working and engaging with industry, right? It’s interesting. There’s sort of a broader interagency effort to actually make this happen. They then pass it over to the FCC to implement. And so, we’ve been working sort of closely with industry partners as they come in and try to navigate these new regulations, and I think that’s been a kind of productive relationship there.
David Feith:
You mentioned the interagency genesis of the drones action. What about the statutory one? What about Congress’s interests over the years? How much was that a factor in having a fairly specific piece of legislation that seemingly put the administration on a clock with respect to drones?
Adam Chan:
Yeah, no. Well, so it is a question. I mean, there was, in the NDAA of 2025, section 1709 did have a provision sort of requiring an addition to the covered list of equipment and services produced by sort of two named entities and their affiliates and subsidiaries, basically required a determination be made whether those equipment and services pose unacceptable risks, required a determination within one year, and if there was no determination, then the FCC would have to add it to the covered list anyway. So, I think the administration was cognizant of that, and that obviously encouraged a sort of broader analysis of the risks from drones beyond simply those produced by sort of any specific named entities. So, I think that might have explained some of the timing. I think now you’ve seen on routers as well a couple of weeks ago, I think the administration sees this as a potentially valuable tool to help address sort of national security risks of these critical technologies.
David Feith:
Well, tell us more about routers. I mean, the second kind of whole sector affected by an FCC judgment in one of these sectoral covered listings. What was the genesis there? What is a router anyway? And where’s this going?
Adam Chan:
Right. Yeah. So, genesis there, I think once again, it was sort of similar process to drones, similar scope of sort of routers produced abroad, unless you get conditional approval from DOW or DHS. I think of note here, I think the sort of determination listed sort of broadly to national security risks similar to drones. One is, once again, the sort of economic security type concern, that routers are just critical to how Americans access the internet, sometimes have like phone service in their homes. We need to be able to produce these devices at home or at least have secure supply chains. And then the second is sort of traditional kind of cyber espionage risk. I mean, we’ve seen the termination talk about recent cyber attacks like Salt Typhoon, Volt Typhoon, that actually based on sort of publicly available reporting, have actually used kind of routers to access the broader telecom networks, posing obvious sort of national security concerns. So that’s how I think sort of routers was chosen.
It’s funny, you ask, “What is a router anyway?” That is something that we are trying to provide as many sort of FAQ-style answers as possible as we get questions from industry. But the definition in the determination relied on sort of NIST definition of a sort of home router. So, it’s a consumer grade router primarily intended for use in a home. So, this is not covering something like sort of enterprise grade routers that would sit in the sort of core of the telecom networks. This is the sort of little box in your home that gives you access to the internet that are often installed by the big ISPs or telecom carriers.
David Feith:
With respect to other sectors of possible significance, I mean, I think you mentioned earlier in general, the authority can cover anything that ranges from computers to phones to modules. What about certain aspects that would seem especially important to critical infrastructure and national security like power inverters in the grid? We’ve all seen sort of valuable reporting about some of the quite obvious national security vulnerabilities in the kind of origin of a good share of the power inverter hardware that we have in various places across our grid. Is that as obvious a concern inside the FCC as it seems from here?
Adam Chan:
So, I guess in answering that question, I mean, I think starters, like once again, we are not the ones who decide what goes on the covered list. So, if I thought sort of power inverters are the most horrible threat we’ve ever faced, it would not allow me to add it to the covered list. But I think sort of interagency is definitely looking at this tool, the covered list, looking at sort of potentially, does it make sense to use it again? Obviously, FCC, we’re not going to be responsible for that decision, but I think it is something like a lot of people both in government and obviously in our conversations with industry, people are thinking about. I’d imagine as we saw with drones and routers, those are two sort of sectors that have long have gotten the attention of national security professionals. I mean, whether that’s sort of reports, whether it’s statements from government officials, whether it’s letters from Congress.
So all that to say, I mean, I’d imagine that if this sort of tool is used again, it would follow sort of potentially similar pattern, where there would be . . . Sort of looking at technologies or sectors where sort of similar kind of obvious national security risks are present, both on the sort of cyber espionage disruption level, and then also on the level of sort of critical supply chain dependencies that we have.
David Feith:
Well, I guess I’ll take the bait a little bit on the suggestion that there’s some value potentially in kind of public reporting as well as statements from various corners of the government.
One area that I know some folks here have been looking into is the combined problem of crypto mining data centers that we have all across the United States, seemingly hundreds of them, that rely on Chinese-origin hardware. Many of them are also owned and controlled by Chinese companies. That is a major concern, partly because these crypto mining data centers draw so much power that they can threaten the grid at major scale. And it would seem, though, that this concern about crypto mining data centers is actually potentially growing into a broad concern about data centers in general, to the extent that data centers in general also are being built with power inverters and optical transceivers and even servers and other hardware that, likewise, are exposed to kind of untrustworthy foreign origin and remote access compromise.
Is data centers then kind of another relevant sector or category of concern that could sort of trigger some of the scrutiny that we’ve been talking about, that obviously has looked so far in other areas?
Adam Chan:
Right. So, I’m not sort of commenting on anything about sort of covered list in particular, whether the administration’s considering that. I mean, I know as a general matter, the data center issue is, one, like we’ve looked at, we’ve certainly gotten a lot of comments on that, and they’re sort of very tied in with sort of core sort of traditional telecom networks that provide services to data center, both kind of wireless and wireline, and sort of looking at . . . So, we’ve definitely been taking a look at this issue, taking a look at sort of providers to data centers, et cetera. But yeah, certainly public is welcome to weigh in as well.
David Feith:
Sure. I know one thing we’ve talked about separately that I’d be curious for your take on is some of how the Trump administration’s America First investment policy about 15 months ago has played out and sort of been relevant to FCC authorities, especially with respect to Team Telecom.
Adam Chan:
Yeah, no . . . Well, so I probably should have answered this in response to your question about data centers. But one area where we have been very active is on the undersea cable front, which actually has a sort of major data center nexus because undersea cables are sort of the unsung heroes of the kind of AI infrastructure build, which is sort of billions of dollars a year, where undersea cables are sort of key to internationally connecting data centers to other countries.
I know definition of undersea cables in the statute is broader than I think sort of some people imagine undersea cables to be, where they just think of the portion underneath the ground, but it actually, we sort of defined it in our rules last year to include submarine line terminal equipment, which is sort of the equipment that kind of connects the cable landing station to the sort of broader data center. And so insofar as sort of we’re looking at the security concerns associated with undersea cables, that very much involves us looking at concerns by those who sort of own and operate the SLTE, the equipment in the SLTE. That obviously implicates the data centers there.
I think on the America First Investment Policy, which is sort of the kind of overarching strategy with which we approach the undersea cable rulemaking, and Team Telecom more generally, I think like our read of the American First Investment Policy is, look, foreign investment and investment generally is good, is a positive for the country. This also plays into Chairman Carr’s Build America agenda, which is all about sort of building infrastructure, enhancing investment in US telecom and related infrastructure.
However, at the same time, like foreign investment can pose obvious risks, especially from certain foreign adversaries. So I think as we saw in sort of undersea cables and as we’re thinking about Team Telecom more generally, it definitely is sort of thinking about this in sort of a three tiered approach, where rather than sort of, I should say, sort of going back for those who are less familiar with how Team Telecom operates right now, but right now. . . who are less familiar with how Team Telecom operates right now. But right now, much in the same way that more famous CFIUS operates, any foreign investment or any international undersea cable, any application for a license for international telecom services get referred to Team Telecom, and they do their standard process review. We think it makes sense to not necessarily treat all applications and all entities applying the same, but to have maybe certain entities, meaning in the undersea cables entities on the covered list, entities controlled by foreign adversaries that would not even get referral to Team Telecom, because it’s just sort of presumptively denied. Whereas maybe there should also be some entities in line with the America First Investment Policy that some applications that shouldn’t even get referred to Team Telecom because they should just be presumptively granted. In that sense, it’s two-pronged that we want to actually deepen our relationships with allies and partners. We want to expand investment in the US without raising the kind of risks that foreign investment has sometimes in the past exposed.
David Feith:
Let’s stay on allies and partners. What’s the international angle here? Of course, the FCC has a certain extensive set of international relationships and obligations, I know some of which we’ll hear about in detail in a few minutes from some of your colleagues. What has been the international aspect of say the covered lists inauguration and these first actions in particular? Is there coordination ongoing with our most important allies, trading and technology allies and military allies on things like drone supply chain issues? Where does the FCC fall in that sort of diplomacy? Presumably, the State Department and others would have a piece as well, but what about the international angle?
Adam Chan:
The FCC is very active internationally. You’ll hear more from Tom, but we have our own diplomats that both have been long active on the trusted networks abroad, in ITU, International Telecommunications Union Standards setting, very involved. More recently, we’ve also been active as well. For example, we have the Bad Labs initiative, which looks at untrusted labs in foreign countries. As part of that, we’ve seen we have mutual recognition agreements with a variety of countries that are reciprocity agreements, where we both mutually recognize each other’s labs, each other’s testing and standards. We’re looking at doubling down and strengthening those and really weaning into mutual recognition agreements to deepen ties with other countries, as long as they are reciprocal in nature. Other countries are willing to treat our technologies, our labs similarly.
On the covered list, I think it’s been very interesting. In last week, we had two briefings at the State Department with different sets of embassies who have been interested in some of our recent covered list actions, who are interested in both learning more, understanding, also looking for ways. Companies from their countries can get conditional approval, can start selling into the US market, interested in the intelligence that led to some of these decisions. Those have been some interesting conversations and those are often with different interlocutors than the FCC has traditionally dealt with, where we have already existing very strong partnerships with our telecommunications regulator counterparts. It’s actually in London last November for our annual Five Eyes gathering. I think upcoming one this year we’ll actually be hosting, which will be exciting.
But additionally, I would say, in addition to the embassy diplomatic outreach, also been engaging closely with foreign companies directly. I know actually, just since our drone action, we’ve had a few of the leading CEOs from Ukrainian drone companies, which are some of the leaders in drone technology, eager to potentially invest in production in the US to enter the US commercial drone market, especially after the fighting stops. Ukraine has pretty advanced drone industrial base now allowing us to leverage some of that expertise. If they onshore production to the US could potentially be valuable in all sorts of civilian contexts, because small drone delivers a bomb, small drone can also deliver your dinner.
David Feith:
Actually, you sort of predicted where I was inclined to go on the kind of international piece, which is, we’ve got a fairly major war underway in the Middle East. How has the Iran war, including its demonstration of perhaps something of a revolution in military affairs around drones affected things at the FCC? You mentioned Ukraine. I was in Taiwan a few weeks ago and was bowled over to learn. I believe the numbers are that Taiwan produced 10,000 units of drones in 2024 and about 125,000, more than 12X in 2025, most of which evidently were for export to Europe through, I think, Poland and the Czech Republic, and effectively, then into the fight in Ukraine. We’re living through quite a moment on drones. Perhaps Ukraine 2023 forward was a first turn of that revolution. It would seem that Iran and Shahed drones hitting infrastructure, public and private facilities across the Middle East is another. Obviously, there are huge questions about counter UIS capabilities and their regulations and licensing. What are the main ways that some of what we’re seeing in Iran with respect to drones touch the FCC’s work?
Adam Chan:
Right. I think it goes to show the importance of having a resilient and strong domestic drone supply given how, to your point, I’m not a military expert, but certainly seems obvious to me that drones, unmanned systems, autonomous systems generally, autonomous systems in large quantity are critical to modern warfare, and therefore, critical that the US is able to produce them. I’ll say, it was actually just, I think last week that Chairman Carr was actually at a test demonstration with Anduril where they were testing out some of their autonomous systems. We also announced this broader kind of drone dominance initiative in line with the Trump administration’s drone dominance executive order, looking at a range of ways, “Okay, now that through the covered list, the FCC has taken this pretty dramatic action to sort of keep out untrusted drones going forward. How can we actually accelerate the deployment of trusted drone technology in the US, and whether that changes to spectrum rules, accelerated experimental licensing terms, all of those sorts of things that can hopefully make it easier to experiment on drones, develop drones, deploy drones in the United States for trusted suppliers going forward.
David Feith:
Related to drones, and I should say, we’ll open it up to questions from the audience in a moment. I’ve got two more for you, if I can take the privilege. The distinguishing between drones and the vast category that we sometimes call robotics or embodied AI, these are obviously very overlapping commercial sectors, technologies, and they pose often overlapping and rhyming national security threats. What about robotics and embodied AI in the FCC?
Adam Chan:
Currently, I don’t think the FCC has a robotics embodied AI specific agenda. It’s certainly something we’re aware of, we’re tracking. I think one point is in the 6G world, faster speed, spectrum communications. Obviously, has a potential for robotics in a whole range of uses, especially industrial uses. But it’s also, there’s obvious national security implications much in the same way as unmanned aircraft systems would seem. I know the broader administration is interested in robotics. I know NTIA had a round table on robotics a couple of weeks ago. I think working with industry, I think we’re happy to pitch in on that as well.
David Feith:
Tell us a bit more, if you would actually, about 6G.
Adam Chan:
6G spectrum discussions generally are maybe thankfully mostly outside of my portfolio, but it definitely is a high priority of the chairman. I know we’re obviously, with this administration and after One Big Beautiful Bill Act now able to auction off spectrum for the first time in a long time, we’re working a lot on World Radio Congress is happening next year, where we’re working to help shape standards, like international standards in 6G. So I think that definitely remains top priority for the FCC and broader Trump administration.
David Feith:
Final question before we open it up. Tell us, what’s been the most fun aspect of the job, and is it data centers in space?
Adam Chan:
Right, right, right. Well, we did put out pretty fun public notice on that a couple of weeks ago. I think the most fun part of the job is just how varied and different every day is. I think the great thing about my job is I get to work with like all the different parts of the FCC and great colleagues, some of which you’ll hear from across the commission, who are doing like very interesting work in a whole range of different areas and a whole range of different technologies. Even as I’m also often meeting with interagency or White House counterparts that have very different outlook, even as I’m also often meeting with a lot of industry players that have very different outlook, and so get as full a picture as possible at the different, whether it’s the different technologies or different policy areas we’re working on.
And so, I think the FCC is sort of unique in that sense because like way more than other national security agencies, we have a much greater relationship and engagement with industry, whereas also like to a greater extent than some just pure economic analysts or industry players, we also engage deeply with the engineering and technology, as well as with the national security, intelligence, that kind of thing.
David Feith:
Let’s open up. We’ll have a mic accessible. Please, introduce yourselves, and try to end the question with a question.
Audience Member Demetri Sevastopulo:
Demetri from the Financial Times. Adam, can you talk about what are the most challenging things from a security perspective that you’d like to do, but that are difficult for either internal reasons or external reasons? What do you think are the sectors that are not getting as much attention as they should from a security perspective?
Adam Chan:
Yeah, it’s a good question. I think from the most challenging areas to get at, I’m not necessarily going to take the bait on specific sectors that are like a target list thing. But I think, as a general matter, the most difficult problems are problems where there are the largest supply chain dependency issues, because for the most part, other cyber type vulnerabilities are ultimately patchable or you can replace old equipment, you can do software updates, that kind of thing, where you can even rip and replace untrusted gear in . . . Some of these things require developments of new technology. That’s something the US is very good at, innovating new technologies, whether that’s in 6G or otherwise.
The harder problems are problems, such as we discussed with drones where the US just doesn’t make the devices. And so, it becomes very difficult to solve a lot of problems when there’s some technology at issue where the US just doesn’t make it. I know we saw this actually several years ago when it came to the 5G infrastructure that like there just weren’t American replacements for say Huawei and ZTE gear. And so, it did lead to a broader issue. There are other sectors like that now where the US has, for decades, focused only on the innovation side without actually thinking about the manufacturing industrial side. I think the hardest national security problems are where we really need industrial supply chain resilience solution and maybe don’t have one and that’s harder, and it’s also harder for the FCC specifically to address because we, unlike other parts of the government, even though we can try to work with them, we don’t have large amounts of money to give out to incentivize production or something like that.
Audience Member Jeremy Zucker:
Thanks so much for being here today. I’m Jeremy Zucker from Eagle Wireless. I’m curious for your perspective from a process perspective on the way in which, for example, the connected vehicle rule was developed over an extended period of time with opportunity for public comment, and then say the recent action on routers, which involved less opportunity for interaction with the public beforehand, and how you think that impacts the ability of industry to react.
Adam Chan:
Well, I will say just having experienced the last couple of weeks, there’s certainly been plenty of opportunity for interaction with industry afterwards, but I do think that . . . I think to your point, I think the connected vehicle rule is like obviously, somewhat different model, different administration, different agency, different authorities. Also notably, that relies on an executive order or a couple executive orders covered list has statutory authority, which is different and has a lot of different kind of process, potential issues there. I think, to my mind, I think both are effective at potentially different ways. I know I’ve talked, actually had multiple conversations with some of your colleagues even since the routers action came out, but I think to the point, something like connected vehicles, which is very large, complex supply chain, maybe makes sense to do extensively phase in over time, talk a lot with industry ahead of time.
There are other national security problems that I can imagine, like it’s important to actually address very quickly where the covered list, I think one positive thing about it is it does actually allow the administration to move quickly. I will note, of course, covered list, it actually is not quite as sort of sudden as some people in industry make it out to be, because it does only affect new models. Right now, we’ve seen with drones and route, the US doesn’t make a lot of routers right now, but people can still go out into the stores, buy routers, router prices have not gone up. We’re like four and a half months into drones now. Nothing horrible has happened since then. I think that’s in part because there is this sort of like phase in built-in. We can actually engage industry a lot on the backend to both encourage manufacturing and onshoring, encourage applications for conditional approvals, that thing that actually allows the sort of transition period to happen in much the same way.
David Feith:
Rick.
Audience Member Rick Lane:
Hi, Rick Lane. Thank you for everything you’re doing on the China front, the work that you’re doing around routers and everything else and drones. My question is, since ByteDance is still controlling the algorithm on TikTok US, and also has changed their geolocation standards, so they can track their users within three feet, is the FCC looking at the possibility of the national security threat of a distributed denial of service attack on cell towers or WIFI systems that, because now they could track everyone in here and they want to shut down Hudson’s WIFI and they create, because they control the algorithms, they control the back office stuff. Is the SEC looking at that now that this is ongoing and the current companies are ignoring the federal law?
Adam Chan:
Right. I said earlier that potentially thankfully 6G is out of my portfolio. I can definitely be thankful that TikTok is also out of my portfolio. Don’t have anything to add on that. I worked on TikTok issue in a sort of former life on the hill. I’ll say, in general about denial of service attacks is certainly something that the FCC is focused on, is thinking about as part of broader cybersecurity type risks. I know we doubled-down on engagement with a lot of the carriers on actually how they can beef, one, like beef up cybersecurity standards, also coordinate more closely like them and with interagency counterparts on a range of cyber response and resilience measures. I think we even announced today, I think we’re hosting some next month, some cybersecurity workshops, and so definitely working to sort of expand or enhance cyber resilience.
Audience Member Savannah Schaefer:
Thanks. Savannah Schaefer, WBK. Adam, thanks for the remarks. You talked a little bit about the enumerated sources in the Secure Networks Act at the beginning, and there are a number that are hyper-specific, like you can amend the section 889 of the NDAA. The executive branch interagency body with appropriate national security expertise is one that’s a bit broader and perhaps less defined. I’m wondering if you can share a little bit about how you guys assembled the Avengers, so to speak, and what that process looks like. Is it an ongoing group? Is it ad hoc? Anything you can share about that?
Adam Chan:
Right. I think this is the interagency body with appropriate national security expertise. I believe 47 USC 1601B1 for those following at home.
David Feith:
You’re the lawyer.
Adam Chan:
Right, right. The statute gives one example, which is the FASC. The FCC has also in the past used the example or relied on Team Telecom determinations, which is another standing interagency body. I think several additions to the covered list were on the basis of a Team Telecom determination of unacceptable risks. I think, as a general matter, it’s our legal interpretation that any interagency body with national security expertise, whether that’s like a standing body, like formalized body, like the FASC and statute or Team Telecom and executive order, or just like an ad hoc grouping. I know, for example, in the recent determinations on drones and routers, the determinations referred to the assembly of like that the White House had assembled an interagency body. Would note we’re not the Avengers assembler, but I think once the agencies have collectively agreed, then would think that would be an interagency body.
I think the statute was deliberately or at least is vague on the point. There are other points where it says appropriate national security agency in B4, and that enumerates five specific agencies. They could have left that general, but there there’s like a specific list of agencies. When they talk about interagency body with appropriate national security expertise, I think that is meant to be flexible for whatever comes.
Audience Member Philip Gunn:
Philip Gunn with the Washington Export Council. Thanks for doing this, Adam. Your work’s really important. You mentioned experimental licensing terms, and I saw that you did that a little bit with the routers issue. Do you think that you can expand on that at all into what that might look like in the future?
Adam Chan:
Sorry, are you talking about the conditional approvals?
Audience Member Philip Gunn:
Yes, exactly.
Adam Chan:
Yeah. Conditional approvals, basically while, for example, for the routers or foreign produced routers are, in general, prohibited from authorization for import or sale. There is an exception for if you can get conditional approval from the Department of War, Department of Homeland Security, I think it’s sort of all the interactions I’ve had with companies with questions about these is very much to encourage companies to apply for conditional approvals. I think there is, I know we already have announced initial batch of conditional approvals on drones. I think we’ll have conditional approvals on routers shortly. I know there have been several applications filed. Ultimately, the FCC, we don’t get to adjudicate those, but I know I see the adjudications by the agencies that matter. I know they have recently gotten more funding, and so there’s now very much sort of formalized process set up to do these evaluations.
And I think there’s definitely a desire among all parties, both in government and industry, for these reviews to be moved very quickly, certainly no more than weeks at the most. And so, I think that certainly, it’s our view, certainly support granting conditional approvals, certainly encourage applications for conditional approvals. If there are trusted drones, trusted routers that don’t pose national security threats that have submitted the application, have the onshoring plan, et cetera, then we’re happy to remove those from the covered list.
David Feith:
Why don’t we wrap it there then? Thank you, Adam. We will move now after a little bit of stage managing to our discussion led by my colleague Michael Soblick with four of the FCC folks who work with Adam on the council. But thank you, Adam, and thank you all.
Adam Chan:
Thank you.
Panel Discussion
Michael Sobolik:
Thank you so much for sticking with us here at Hudson. Thanks for coming to this excellent event and this conversation about the FCC and their national security work. My Hudson colleague, David and Adam, thank you for that wonderful conversation that we just had. We are now going to speak with a number of Adam’s colleagues at the FCC and drill in and zoom in on a number of the elements that David and Adam just talked about in the fireside chat. Up here with me on stage, really excited to begin this conversation with a collection of seasoned and really wonderful national security professionals from the Commission. I’m going to be introducing them. We’re going to keep the audience guessing here, so I’ll show you where they are, but this will not necessarily be in order of where they’re sitting. Zenji Nakazawa. There you are, Zenji. Hello. Zenji is the Chief of Public Safety and Homeland Security Bureau of the FCC.
Thomas Sullivan, far end over there. Hello, Thomas, the Chief of the Office of International Affairs, FCC. And then to my immediate left, Hunter Deeley, who’s Chief of Staff at the Enforcement Bureau. And then Alice Jou right there. Alice is Deputy Chief Office of Engineering and Technology. And between the four of us and the great initial conversation that precedes our conversation, I’m excited for what we’re going to dig into. So Zenji, I want to start and turn to you with a question, picking up where David and Adam left off. I was chuckling to myself when Adam said the FCC, we’re not the Avengers assembler, which in that specific sense, that is correct. But the FCC, as an institution, is a bit of an avenger itself. The energy and the presence that the Commission has had recently is quite impressive and extraordinary, not just within the United States, but globally with allies and partners, as they discussed previously, we’ll get into that as well.
But I want to ask you about the situational placement of the FCC, because I think as is clear from the conversation that precedes ours, you can’t really talk about the work of the FCC without talking about Team Telecom. I think this is an interesting point of the FCC that can often be overlooked, that as energetic and as important as the work is, that the Commission does, y’all are downstream of policy decisions that are made within the inter-agency that then empower the Commission to do very specific things. So that was discussed at a broad level. I want to get a little more specific. Can you talk about Team Telecom, what that actually constitutes? Who is involved in that collection of agencies? And not just the triggering mechanism that empowers you guys once a determination is made by Team Telecom, but even day in, day out, how you work with those agencies on the regular.
Zenji Nakazawa:
Yes. Happy to do so and a pleasure to be here. Thank you so much. So, the FCC, we are a regulatory agency. We regulate telecom for wire and radio communications domestically as well as internationally. So, when folks want to operate within the FCC, within the United States, or get a license, they have to apply for an application. So those applications, when they come in, they are not summarily granted. We do, depending on who the applicant is, we do look at the application and analyze what service they want to provide, who they are, et cetera. So, stepping back, the FCC, we are a convening agency. We don’t work in a vacuum. We work with other agencies and stakeholders in the federal enterprise. So that is with, of course, the White House, but with other federal agencies from Department of Homeland Security to the Department of War, also with the USTR, et cetera, Commerce.
So, when these applications come in and they do raise that kind of an issue that raises a red flag, it is something that we have the capability to refer to Team Telecom for further investigation and analysis. And depending on that analysis that does come back from Team Telecom, which is comprised of all of these federal entities combined together, we do make an action on that application before us. So sometimes the application recommendations will come back from Team Telecom saying, “Fine, no problem.” Another instance, it could raise a flag and say, “This is problematic.” And it can be however solved or mitigated if certain conditions or factors were put into play. And if we get that second type of flavor, then we would go and analyze the application and grant it, making sure that those types of conditions are implemented and specified in the ongoing document.
And of course, the third one is where it would be a flat categorical no-go red light, that you please do not accept this application. So, Team Telecom plays a very vital role in our work because just by nature, as a regulatory agency, we are not a national security expert per se. We are not classified as an agency with national security expertise, so we do rely on the internet agency heavily. So that’s Team Telecom in a nutshell.
Michael Sobolik:
The conditional approval that you talked about and that Adam mentioned as well, I think this is worth getting into more because you can’t listen to a structured solution like that and not think of CFIUS, where in CFIUS, you can have a mitigation agreement that allows a deal to go through while also having some sort of safeguards and standards in place. And in the context of the FCC, I think maybe Hunter, maybe this will be a good one to kick over to you. Could you unpack and maybe provide some examples of conditional approvals, not just on how those get structured, but even on the enforcement side, like how to make sure that when a conditional approval is granted that those standards are actually being adhered to?
Jeremy Zucker:
Yeah, sure. First, thank you for having us and really enjoyed at the fire side before this. As Zenji mentioned, during the course of a team telecom review, there’s this middle ground. So, the Team Telecom agencies identify a risk to national security and law enforcement interests. What they do there is then identify certain terms that would mitigate that risk. They turn around and they say to the Commission, “We don’t object to you granting that authorization so long as you condition the granting of that authorization on compliance with this mitigation agreement.” Why this is particularly topical in the context of the Council on National Security this year is with amid the backdrop of the Council and the using that as a forum to coordinate both internally and externally, we took the first ever enforcement action against a regulate for violating the terms of their license, the condition of the license, and that condition being complying with a Team Telecom mitigation agreement.
We used the council itself to coordinate internally between the Enforcement Bureau, the Space Bureau, and the Office of International Affairs in this instance. It involved a regulate that had both in 2000. . . I’m sorry, 2022 had been granted an international Section 214 and several Earth Station authorizations. As part of that grant, they agreed to abide by certain conditions with team telecom agencies, including DOJ. And one of those terms required them to seek advance approval from DOJ before providing foreign employees with access to their network.
Michael Sobolik:
Interesting.
Jeremy Zucker:
They didn’t comply with that term. They actually granted access to 184 out of 303 forum-based employees without first seeking DOJ vetting approval. We also used the Council as a forum to coordinate with DOJ itself. DOJ, under their obligations for monitoring that Team Telecom mitigation agreement, they first did an investigation, they built a record, and then they shared that information with us at the FCC. That allowed us and the enforcement bureau to then kick off our own investigation, develop our own record, and we were eventually able to settle that investigation with the company for approximately, I think it was close to $200,000. And then importantly too, a consent decree that added additional compliance terms on there.
Michael Sobolik:
Gotcha.
Jeremy Zucker:
I think it was important for a couple of reasons. One, it showed how the Councils facilitated some of this coordination that we’ve been talking about. Two, it showed that coordination both internally and externally. Two, it was a reminder to the industry and to regulate that signing up for these agreements when you undergo a Team Telecom review is not just a checkbox. They are designed to mitigate identified national security and law enforcement risks. And the Commission, particularly with the Council of National Security, has made it clear that these are important commitments and we’re going to prioritize investigating them.
Michael Sobolik:
Speaking of investigations, not just with enforcement too, beyond these conditional approvals, could you speak more to the other types of actions, either with investigating or with penalties or what have you, what other actions have you taken recently along the way?
Jeremy Zucker:
Yeah, sure. So concurrent with announcing the creation of the Council on National Security, the Chairman also announced what was the largest investigation into cover list entities in the Commission’s history. We kicked it off at the same time as the Council’s creation. We issued letters of inquiry and subpoenas to nine of the entities on the covered list, investigating what they were doing here in the US. Were they complying with the various restrictions that come along with being named on the cover list? Were they offering services here that would otherwise require a FCC authorization? Were they selling or marketing equipment that either was not authorized? Were any of these entities finding a way around these restrictions? Just like the Team Telecom action, we have been able to use the Council on National Security as a forum for what we’ve learned in the course of this investigation to share information with our partners throughout the Commission.
We’ve been able to get the information into the hands of the licensing bureaus and offices quickly to help inform them, to fill any gaps that they’ve identified in the Commission’s rules. We’ve taken this information and we’ve also been able to, when we’ve uncovered violations, take action. Earlier this year, back in February, we issued a notice of apparent liability against Zhejiang Dahua for approximately $188,000 for the company’s failure to file a updated list of subsidiaries and affiliates as required under, I think it’s section 2.903. I shouldn’t have started down that route. Adam did such a good job earlier rattling off. I wanted to impress him. But we did that. If these entities are not following the rules and we find sufficient evidence to justify it, we’re going to take action there. And then we’ve also been using this information to work with interested stakeholders outside of the Commission too, whether that is law enforcement partners like the Team Telecom agencies or leading e-commerce sites that we have been working with through what is, we’ve called Operation Clean Carts.
That’s been an effort to work with these platforms to pull down listings of unauthorized or illegal equipment, that includes covered equipment and also illegal equipment like jammers. Thus far, we’ve able to work with them to pull down over three million listings of unauthorized or illegal equipment.
Michael Sobolik:
Wow.
Jeremy Zucker:
So, it’s been a success over the past year.
Michael Sobolik:
Thank you for sharing that. That’s great. I want to turn now to Alice and get into something that Adam mentioned in passing, and I think it was worth digging into a bit more. I will say maybe at the risk of embarrassing myself publicly, the FCC sticker that Adam talked about, I literally did not know those things were real until recently. So please, thank you for sharing a stage with me despite me not knowing that. But I want to ask you about that because the certification for a lot of these equipment, as Adam was briefly mentioning, I think it’s easy for Americans to assume that these things are certified within the United States of its technology that we’re using inside the United States, but that is not necessarily the case. And Adam mentioned the bad labs proceeding. I’d love to hear more about that from you and what the FCC’s work has looked like there.
Savannah Schaefer:
Sure. And thank you for having us here. And before I go further, let me just brag a little bit about the Team Telecom expertise we have at the FCC. Both Hunter and I are alums of Team Telecom of DOJ’s National Security Division. Hunter, before Team Telecom was even formalized, he was working on CFIUS for years. I also was part of DOJ when Team Telecom became formalized, and the executive order was passed. And all this to say is for folks who want to give different stories to Team Telecom than they do to FCC, we’ll find out about it.
But also, to going back to why we’re at the FCC. We’ve heard a lot about Avengers. The FCC has a quiet superpower, and Adam mentioned it in passing, but it’s section 302 of the Communications Act, that every single consumer Bluetooth, Wi-Fi, 4G 5G module antenna is regulated by the FCC. It’s regulated consistent with the public interest against the interference potential of devices that are capable of emitting RF energy. So, on this stage right now, we have multiple wireless mics that all work. Those are transmitting pretty high power. In addition to that, you’ve got a lot of low power devices on you, your smartwatch, your phones. Your iPhone has more than a dozen different antennas inside. There’s multiple versions of Wi-Fi, multiple versions of Bluetooth, GPS, Tap to Pay. All of this works. It works because there are 12 people at the FCC’s lab in Columbia, Maryland who are responsible for the equipment authorization program.
And each year that the FCC brings to market over 40,000 new devices that are certified. About 3,000 new grantees or they’re called manufacturers or people who get these authorizations and certifications. And that whole program, even though there’s 12 people at the backend at the FCC, that whole program is largely done by private entities. Certification bodies who ultimately make the decision whether or not this should be certified by the FCC. And there’s about 40 of these telecom certification bodies or TCBs. And before that, there are about 550 test labs that are recognized by the FCC. When you want to bring a device to market, your Wi-Fi, your Bluetooth, you go get it tested at an approved FCC recognized test lab. Then you bring it to a certification body, and then it ultimately enters into the FCC’s equipment authorization program. And that’s the only way a device like your Wi-Fi or Bluetooth can be marketed, imported, or sold inside the United States.
So that to me is an amazing superpower that the FCC has that no one knows about. And talking about the scale, I’m in the Office of Engineering and Technology. Our mission really is to bring all of this innovation to market. So, we are focused on scale. We want to bring new devices, new AI glasses, all of these cool things to market. But when you reach the scale that we do, there are going to be a couple of bad apples that slip through. And that is very much a focus of our, what’s called the equipment authorization integrity rulemaking, which is what we also call bad labs, but it’s really about policing the gatekeepers to our system, the test labs.
Last year, we passed new rules saying that certain prohibited entities shouldn’t be allowed into our program. They shouldn’t be allowed to have control over the test labs, the certification bodies, the lab accreditation bodies. Those rules went into effect last September. And since September, we’ve removed about more than 20 test labs from our system because of the types of problematic ownership, ties that they may have. And we’ve been public about the ones that we’ve removed and withdrawn from our system. Some of them are literally arms of a foreign adversary government. Literally the regulator that approves devices in their country that won’t accept US test results was allowed for years to get their devices approved through our program. That doesn’t make any sense at all. And so, we are continuing to do this process. Currently, the foreign test labs, all test labs, are recognized by the FCC on two-year terms.
They’re two-year terms, their recognitions come up for renewal every two years. We’re about six months into the process, so we’re about a quarter of the way through of all the 550 test labs. We’re finding certain foreign labs decide not to even decide to renew. So we’re discouraging some bad actors from coming under our scrutiny. I definitely want to thank the Enforcement Bureau. This kind of national security investigation really does require a lot of investigations expertise. You have to look at corporate ownership and history and relationships. You have to ask questions of these entities that may not want to answer them, and it does require a lot of coordination. It does require a lot of detective work to find this.
Michael Sobolik
Couple follow-up questions for you about that. Number one, you said so far about 20 labs or so have been removed. Has it been an issue or has it been difficult to introduce, or has there even been a need to introduce new labs into this program to supplement the removal of those? And then number two, is this something that allies or partners have expressed interest in working with the FCC on for them as well?
Savannah Schaefer:
Yeah. So, the first question, has this created a supply chain shortage? Because the testing service is part of the supply chain. It’s the last step before a device can come to market. And yes, because we’ve had a lot of foreign test labs, some of which are not trusted, some of which offer testing services at much lower cost than US or allied partners. And those testing services are sometimes their quality isn’t always great. And so yeah, when you remove 20 from a system that’s a significant percentage. We can expect more to leave in the coming months.
There will be fewer testing services available for devices that need to come to market. And that’s why it’s so important for us. And I just want to thank the Office of International Affairs. We do work with our allied partners and engage with other regulators whose regimes we trust. And as Adam mentioned, that’s what’s called the Mutual Recognition Agreement. We trust other countries because we trust their regulatory regimes.` They will accept our test results, we will accept theirs. It’s very important that we work together with these countries and these regulators. And some of these are allied regulators, our allied partners, are even ahead of the game in terms of finding non-compliance among test labs. And some of our partners overseas have identified test labs where they have found fraudulent test reports being submitted. Sometimes Photoshopped test reports being submitted. They have announced those publicly. We have found regulators that really do want to go more public with some of the discrepancies they’re finding and the discrepancies in quality of these test reports.
And so, it’s very important that we work together with some of these partners and explain that we do need to work together to fill that supply chain gap. It’s not just about bad labs, as you talk about it, but it’s really improving the availability of trusted labs everywhere. So that, because our primary mission, again, is to bring more devices to market, to bring innovation to market.
Michael Sobolik:
Yes. Thomas, did you have something to add to that?
Thomas Sullivan:
Yeah. If I may, and again, thank you for having us here. But I think what Alice just said, I think is an excellent example heralding the one-year anniversary of the Council because through the work of everyone up here plus those in our bureaus and offices, as well as the other bureaus and offices that are not represented, we can bring together these issues in a very timely manner. As OET is doing this under the Council’s auspices, we can also reach out to our foreign embassy personnel, those we have MRAs with, those who we know we might have MRAs with. And this happens between all the bureaus and offices in terms of that cross-bureau collaboration that this Council has enabled. So, I just wanted to bring that up and herald back to this is our one-year anniversary and how much progress I’ve seen coming from the council.
Michael Sobolik
Thank you for saying that. And let’s actually stick with you, Tom.
Thomas Sullivan:
I shouldn’t have said anything. Shouldn’t have spoken up.
Michael Sobolik
No, this is a great segue way. And I think also just stepping back, the interconnectedness of the Council is quite evident from just the comments we’ve had in the first 25 minutes or so here, where all of the actions that each of you have been spearheading depend and rely on the work of the departments and bureaus and offices also represented on this stage. So, I think that comes through quite clearly and it’s something to be celebrated. Thomas, on the international front. In the fireside chat, Adam talked about undersea cables being the, quote, unsung hero of AI infrastructure. And I think a few of the things that Adam said about that make the case about data center interconnectivity and how broadly you think about what these undersea cables are doing.
But I want to talk with you more about this because this is something that the FCC has really invested in in recent months. Beyond data centers, can you say a few words about the Chairman’s prioritization of this issue area and speak a little more specifically to some of the work on undersea cables that you’ve been doing?
Thomas Sullivan:
Yeah. Yeah. Thank you very much for that question. This is a top-of-mind effort across the Commission. The importance, to your first point, of undersea cables, it is essentially the global glue infrastructure. It’s taking the Chairman’s Build America program and putting it onto the global scale. These are the networks that are carrying AI, next generation technologies, all of the data that needs to transit the world. For example, 99 percent of global internet traffic is carried by undersea cables. $10 trillion a day in financial transactions occur across the undersea cable networks. So, at the FCC, we’re wanting to make sure that we are doing everything we can to continue the build out of undersea cable networks from the United States to trusted partners and allies to help on a couple of different goals. One is we need to make sure that we’re enabling a diverse network of routes from the US to partner nations.
If you look at the importance of route diversity, you look at the Baltic Sea incidents, other undersea cable cuts, having redundant and multiple pathways between trusted partners is paramount. So, we want to make sure that we’re doing everything we can to streamline the processing while also keeping security top of mind. The second important aspect with this is we’re trying to meet, from an economic perspective, the current data needs of . . . Perspective the current data needs of other countries as well as their future data needs. So, if you look at the scale of expected demand for undersea cables, it is an exponential growth, especially with the advent of AI and all the data that’s going to need to transit systems. And then of course, making sure that we have opportunities where you have multiple points of entry into particular countries. If you look at the case of Tanga, for example, when they had the undersea volcanic eruption that disrupted their domestic inter-island network, they were out of connectivity for months and months and months, and you need to have these undersea cables to handle a lot of government data, sensitive health information, especially in a lot of the Pacific Island and other island states. So that’s the short answer to the priority, a long answer to the priority issue, but clearly these are paramount for national security, for economic development, as well as for consumer welfare.
Michael Sobolik:
I think it’s important too to step back when we talk about undersea cables. It’s not just the specific technology or the specific issue that matters. I think this is something that differentiates and demonstrates the scope of what this National Security Council has been doing within the commission because up until undersea cables, we have been talking primarily about protect priorities and resiliency priorities. What you are bringing out is this equally important priority of promoting diffusion of American technology globally. And I think Washington can spend a lot of time talking about resiliency and supply chains, which I mean, there are real reasons to do that, but promotion of US tech and making sure that our relationships with our partners and our allies are resilient, that’s equally important. So, I think this also speaks to the multidimensional work that you guys have been doing. Could you say a little bit, whenever we get into conversations about diffusion, there seems to be this perennial tension between making sure that deployment can be done rapidly and quickly, while also making sure that the technology itself is secure.
And this isn’t necessarily unique to undersea cables, but I’m sure it can be manifested in that context and certainly in any other realm of tech conversations we have. So, could you speak with undersea cables how you go about managing that tension?
Thomas Sullivan:
Yeah, it’s a great point. And in 2025, we took a look at our rules, came up with a report and order and to further notice of proposed rulemaking at the commission under Chairman Carr’s leadership to do both, to make sure that we were doing everything we can to both modernize and streamline our regulations, which hadn’t been updated for over 23 years to that point, but also doing so with security and national security top of mind. And here’s a couple of points of how we are striving to achieve both. Looking at the team telecom process that we’ve talked about here as an example in the undersea cable realm, we’re looking to essentially codify a lot of the requirements that were recommended to the FCC to attach as conditions of licenses and make them kind of primary upfront and have applicants attest to their adherence to those upfront as part of the application instead of a longer backend review by Team Telecom.
We’ve also worked with Team Telecom collaboratively to come up with some standard questions, and we continue to look at those as risks evolve and they collaborate with us and our partners up here on those as well. We’ve also included some key factors in our rules from last year. As Adam noted these upfront, it’s like a presumption of denial from foreign adversary applicants. We have a presumption of denial from landing points there. We’ve incorporated some key national security requirements upfront in our new rules and notably as part of a further notice from last year, we’re looking to create the fast lane that Adam and the chairman are conceiving, where we have our trusted entities from the US, frequent filers of applications, so we know the ownership, we know the equipment they’re using is not on the covered list.
We know the ships that they’re using to deploy to give them a fast approval and knowing that that’s happening with national security top of mind and creating another lane, I won’t say a slow lane necessarily, but a pathway that has to go through a more strict review if there’s any unknown or concerning ownership or equipment interests as we’re building these out.
So, I think we’re landing in a really good place and I’m really proud of the work from my team and the team across this table, as well as everyone on the security council for getting this work done. I think it’ll be very helpful for the industry and for the United States as we go forward globally.
Michael Sobolik:
Thomas, at least for now, one more question for you. I think it’s natural when you talk about allies and partners, not just to discuss the efforts that are coming from the commission and from this council in particular, but I’d love to hear about the reception from partners. Over the past year for the work that you guys have been doing, what’s the feedback been? What’s the reception been?
Thomas Sullivan:
It’s been, I would say, outstanding, unless you’re a foreign adversary, but to the point of outstanding, I’ll sit back. Many of our Five Eyes Allies really are taking strong note of the work that we’re doing across the commission because we are taking a really comprehensive look at security across all factors of a regulator, as NG noted. And it’s something that some do, but not every global regulator does. And it’s part of the work that the chairman has encouraged us to go forth and help expand. He talks about this himself when he meets with ministers and foreign regulators, and it’s really about the importance of incorporating national security priorities as part of your regulatory and policymaking decisions. And whether you have a formal mechanism for getting that information globally or an informal mechanism, I think the lessons that we’ve globally learned from incidents like Salt Typhoon, Vault Typhoon have really given a wake-up call to the world.
Global communications ministers are usually the first ones who get the call from their heads of state when something like that happens. And so, they do reach out to the US government and we work collaboratively with the state department, has a number of programs that we can help talk about best practices. It’s through something known as the DCCP, Digital Cybersecurity Connectivity Program. Department of Commerce has another great program where experts from the US can go abroad and talk about these issues, the Commerce Law and Development Program. Of course, there’s USTTI, the Training Technical Institute that falls under the State Department umbrella. And then we have within the FCC, the International Visitor Program, where we have my team can go out and try and get regulators, make them aware of issues that we’re doing. If they want to hear more about any regulatory or security issue that we’re dealing with, we can brief them virtually or host them at the FCC.
So, we’re seeing a lot of activity as a result of the council. It’s good for business, as they say. And I think it’s a really good sign that we’re getting a lot of positive feedback globally because countries are making these efforts and wanting to make these investments in their own security posture.
Michael Sobolik:
Zenji, back to you for, I guess, more of a retrospective and maybe even an introspective question. We were chatting earlier and you had mentioned that you had been present and involved in some of the initial uses of the covered list a number of years ago on specific entities. I’d love to hear from your vantage point, not just over the span of any number of years, but particularly within the past year with this commission and the work that it’s done, can you say a few words about how the impact of the covered list utilization has changed, how it compares to what it was like previously and how it maybe dovetails with some of the other elements that your colleagues have been talking about?
Zenji Nakazawa:
Yeah, sure. Good question. And how much time do you have?
Michael Sobolik:
How much time do you have?
Zenji Nakazawa:
… So really to understand the covered list and to understand how it is most recently been used to reshape the FCC’s role in national security, you have to look at a couple of seminal events that happened before the covered list came to fruition, and then that sort of can inform what’s happening right now so you can get it in context. So, the cover list really isn’t something that operates in a vacuum. As early as 2012, the House Select Committee on Intelligence has already highlighted the dangers of certain foreign electronic equipment and then taking up the banner in 2018 under Trump administration one. In November, the agency put out a notice of proposed rulemaking that basically said we should be paying attention to this, and we should have some types of rules involved to prevent, especially at that time, because as Alice mentioned, 302 is the sleeper cell fantastic magic potion.
But before we became that ingenious, we were looking at just the hit them over the head type approach, and that was with USF, a universal service fund, an $8.5 billion fund to help high cost area development for telecom, but basically saying, look, you can’t use these funds to purchase equipment that is manufactured by certain companies. And at that time in that initiative under Trump one, we designated companies and from there we said that those companies, if you are a USF recipient, you have to rip and replace that equipment, but we are also establishing some sort of a reimbursement program for the equipment that you ripped and replaced. So that’s 2018. So, we have the sense that this covered . . . And we actually called them covered entities at that time. There was no list and that carried forward because shortly thereafter . . . Actually, it was before that, but in that same time period, the John McCain NDAA of 2019 came out that said to basically addressing all federal government users don’t use this equipment.
This covered equipment poses a threat to national security. And it was there in section 889 of the NDAA 2019 that they identified certain Chinese equipment and services as covered entities. So, fast-forward then, like a year after that, the FCC then started their rulemaking to say, okay, we’re going to implement the rules that we proposed and the notice of proposed rulemaking that I talked about before with USF. And we went forward and did that, but Congress and their infinite wisdom also shortly thereafter-
Michael Sobolik:
Phrase that does not get uttered regularly.
Zenji Nakazawa:
Yes. Literally four months after the FCC released their rulemaking enacted the Secure Trusted Networks Communications Act or STNCA as it’s fondly known. And that codified essentially, it was like, who’s codifying what? But we mirrored each other. So, the statute of STNCA, the Secure Networks Act, and what the FCC did, pretty closely mirrored each other. There was conversation there and some coordination, but I think the . . . And this STNCA actually gave birth to the covered list because it was there that Congress said, “Okay, so we know that there are these covered entities out there. Let’s put it on the list. We’ll call it the covered list and it will do all the things that the FCC is already doing, but we’re going to expand that prohibition to not only USF, but all federal funds that are managed by the FCC.” So, you cannot use those funds to purchase these covered list equipment and services.
So fast-forward now, since that time from 2022, when Chairman Carr came in, I always joke with him, I said, “You injected rocket fuel into the veins of this whole process,” because he has taken it to leverage the covered list as essentially a tool that has undergirded a lot of our, well, almost all of our national security initiatives that we’re doing at the commission. And every pretty much like nine out of 10, if you look at all of the important items that the commission has put forward, they tie back to the covered list as a fulcrum point to lever as almost like an ignition key to lever when national security concerns are raised. And I think there he’s made it actionable and it’s been very important because it’s been something that we’ve been missing. I think as Adam pointed out before in 2018, 2019, we had this idea of a covered list, but it wasn’t actionable.
It was limited to a small scope. Then as Alice mentions, and as Hunter mentions, we leveraged it into this beast, really, looking at equipment authorization, looking at equipment enforcement, and then bringing it also to sub cable regulations. And I think that’s really important because it’s worked on two folds. One is we have heightened our cybersecurity posture in this country, but we’ve also created a new avenue for the US government to use in its arsenal to protect itself, but also to become more proactive in its stance when it comes to national security.
Michael Sobolik:
Thank you for that. Before we start our final lightning round here, and apologies to the crowd here, we are on a sensitive hard stop, so thanks for bearing with us. We may not have time for audience Q&A, but I will take prerogative and wrap this up. Before we start doing that, Alice, I actually realized there’s one more question I wanted to ask you, speaking of the equipment authorization program that I did not ask you earlier, could you speak a bit to modular transmitters and some of the work that the FCC has done there?
Savannah Schaefer:
Sure. Well, following up on the covered list, as we’ve mentioned, we don’t make the national security judgments, the national security agencies do, but we apply our communications focused expertise to those judgments. Modular transmitters, if our national security partners say a communications equipment, a modular transmitter, that’s a Bluetooth, a standalone Bluetooth WIFI, 4G, 5G module, if that poses a risk to national security and unacceptable risk to national security or the safety or security of US persons by itself, we apply our judgment to say, “Hey, the module inside a host device could also pose the same risks to US persons, and we shouldn’t be authorizing those either.” And the way I try to analogize this too is, I call it the cheese sandwich rule because if you’re not supposed to be eating the cheese and it poses a risk to you, then you shouldn’t also be eating the cheese sandwich.
Modular transmitter, sometimes these terms get very wonky, but that’s how we’re applying our judgment. We are seeing that there are devices that slip through the cracks again with 40,000 devices we approve that do contain inside of them covered equipment that are modules. And so, we passed new rules last year to start clamping down on the covered list in that way. Just hearing Zenji talk about the history of the covered list, we were on the outside at the Department of Justice in the National Security Division. I remember hearing all of the excitement over, especially with some of our law enforcement partners, FBI agents, they have been tracking some of these companies and have seen very suspicious activities that they thought did pose a risk to national security and to even specific US persons. But was it illegal? Was criminal prosecution really the best tool that we could bring?
Especially if in a criminal prosecution, they would have to prove some of these things beyond a reasonable doubt where all of that evidence is overseas. Can you really do that and is that the best tool? And one thing I think from the outside before I joined the FCC, I did see how the FCC, how even then Commissioner Carr and now Chairman Carr really raised some of the authorities that the FCC had that were even more powerful at deterring some of these bad actions through civil and administrative means that the criminal law enforcement partners could not. Covered list, our equipment authorization program, these are incredibly powerful tools that deter bad actors that are abusing their access to our supply chain, to plant very serious risks to our national security through our own systems. And I’m very proud to see from the inside some of these things that are happening that have been years in the making.
Michael Sobolik:
Thank you. That is a perfect segue into the final question that I want to ask each of you, speaking of being proud about something, I want to ask what David asked Adam, which is number one, what’s your favorite part of the job? And then number two, what are you most proud of for the work that the commission has done over the past year? And if you want to double tap something you’ve already said, that’s totally fine, but maybe we can start with Hunter and then go down.
Jeremy Zucker:
I should have sat down.
Michael Sobolik
Put you on the spot.
Jeremy Zucker:
So, two parts. What’s the most fun part of the job and what are you most proud of? Most fun part of the job to . . . The area that the FCC regulates is so vast. I mean, you’re literally talking sea bed to outer space. Somebody who came to the FCC with a national security background, but not a communications background, I’ve been here for a little over three years now. It has been an incredible experience to learn so much on a day-to-day basis, which then leads into the part that I’m most proud of is sort of two parts.
One, the people that I’m working alongside with, I’m immensely proud and impressed by the work they do. In the Enforcement Bureau, we have, I’d say, operationalized probably four of the six divisions to investigate these types of cases. These are people that may not have previously investigated national security related matters, and to see talented lawyers, engineers, analysts, support staff dive into it has been astounding. And then a tangible case, this team telecom matter that we resolved earlier this year was something that we had been thinking about for a long time, probably the day that I got here three years ago, to see that finally come together, and I think that’s a testament to the council’s work of bringing people into the room and getting heads together and trying to figure out how to make a process work was pretty great. It was a pretty exciting, tangible win.
Michael Sobolik:
Thanks, Alice.
Savannah Schaefer:
Sure. Most fun and most proud of?
Michael Sobolik:
Yes.
Savannah Schaefer:
Most fun, especially in the office of engineering and tech is really to imagine how technology can be used, both for good and for bad. The fun things are, hey, there are new AI glasses coming up, but there’s also new robotics. I’ve seen in other countries, you have robot legs that can help you run faster. And all of these things require more spectrum and more fully loaded spectrum. So, think of that in the positive sense and then in the national security part to think of all the conspiracy tinfoil hat wearing things, there are some very scary uses of all of this innovation. And I find it fun to even think about all the catastrophes that can happen. I just think it’s fun, and to be in a position where we can do something about it, these threats that I had seen from the outside that weren’t appropriate for criminal prosecution but are perfect for an agency that has the powers that the FCC does.
What I’m most proud of, I would say similarly is being able to be part of this council on national security, being under leadership with our chairman and with Adam that wants to be creative about how we do our jobs. We’re not just doing what the FCC has always done. We’re taking what the FCC has always had and applying it to meet the threats of what’s coming up. So I would say most proud of something like Bad Labs that requires us to work with the Enforcement Bureau and the Office of International Affairs and also Public Safety because they’re the ones ultimately who put things on the covered list to see all that come together in this really tiny little agency that national security is just a piece of what we do and yet it has so much more impact than a lot of what I’m seeing outside.
Michael Sobolik:
Thank you. Zenji.
Zenji Nakazawa:
So, for me, every day is like draft day in fantasy football because I get a chance to work with this National Security Council. You get literally the best and the brightest, I don’t know why I’m on this committee, but the best and the brightest on this committee that are applying their expertise and disparate perspectives, bringing in different skillsets and looking at a problem from many different angles. And I think this is the first time that the agency has actually put a lot of effort behind bringing everyone together in one room, at a table, discussing issues, parsing over things all together, and I think that that creates some kind of a synergy that really bodes well for national security at the FCC.
Michael Sobolik:
Yes.
Zenji Nakazawa:
And as far as what I’m really proud of, I’m just really proud of the work that we do. And in particular of late, we’re working very closely with the White House’s FIFA Task Force as well as the White House’s Task Force for LA ’28, the Olympics. And believe it or not, the FCC, thanks to the chairman has plugged us in with senior leadership. So we’re at the table, we’re raising concerns, we’re helping out on spectrum deconfliction issues, as well as spectrum monitoring to make sure that communications are working. And for example, you don’t want Australia and the US going to the finish line in a hundred-meter sprint or swim, and all of a sudden, the clocks go out or something. so, things like that, it’s very meaningful. Thanks.
Michael Sobolik:
Thank you. Thomas.
Thomas Sullivan:
So fun and proud. It’s going to be both about the people that I get to work with every day, including the folks on the council, but also people in OIA, interagency partners. And for me, it’s waking up every day and there’s always new challenges even beyond the security portfolio under OIA that is really interesting work that my staff does. One thing to be proud of is actually seeing very tangible results of what we do on an international basis with other countries adopting similar practices. And there’s been some great examples of that with Costa Rica, Czechia Republic. I mean, we have great relationships with many different regulators who have adopted very fundamental principles going forward, but those are just a few. I could go on and on and on about other countries as well, but I’ll stop there.
Michael Sobolik:
Well, we are deeply grateful as Americans for the work that you guys are doing with the council to keep the equipment with us. Adam, thank you for coming as well. David, thanks for hosting and moderating. And then to all of you, thank you for joining us. Appreciate it.

Please join Adjunct Fellow Daniel Batlle for a conversation with Elliott Abrams, whose leadership on Latin America policy stretches from his service as assistant secretary of state for inter-American affairs under President Ronald Reagan to his role as special representative for Venezuela in the first Trump administration.


Join Hudson as Adjunct Fellow Daniel Batlle sits down with Julio Crespo MacLennan, a historian and one of the leading scholars on Spain’s democratic transition and on Europe’s relationship with the wider world.


Please join Hudson Institute for a fireside chat between Hudson Senior Fellow Nadia Schadlow and Deputy Assistant Secretary for Industrial Base Growth and Director of the Office of Small Business Programs James Mismash.


Please join Hudson Institute Senior Fellows Bryan Clark and Dan Patt for a conversation with Under Secretary of War for Research and Engineering Emil Michael about the Department of War’s efforts to bring AI to the battlefield and implement an innovation strategy that makes the most of America’s commercial and government research sectors.